A new iOS trojan has been found in the wild that's able to infect non-jailbroken iOS devices through PCs without the need to exploit an enterprise certificate. Named "AceDeceiver," the malware was discovered by Palo Alto Networks and is currently affecting iOS users in China.
AceDeceiver infects an iOS device by taking advantage of flaws in FairPlay, Apple's digital rights management (DRM) system. According to Palo Alto Networks, it uses a technique called "FairPlay Man-in-the-Middle," which has been used to spread pirated iOS apps in the past by using fake iTunes software and spoofed authorization codes to get the apps on iOS devices. The same technique is now being used to spread the AceDeceiver malware.
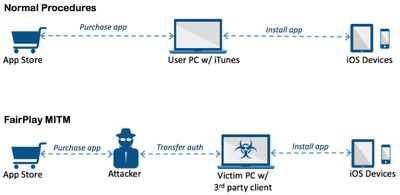
Apple allows users purchase and download iOS apps from their App Store through the iTunes client running in their computer. They then can use the computers to install the apps onto their iOS devices. iOS devices will request an authorization code for each app installed to prove the app was actually purchased. In the FairPlay MITM attack, attackers purchase an app from App Store then intercept and save the authorization code.
They then developed PC software that simulates the iTunes client behaviors, and tricks iOS devices to believe the app was purchased by victim. Therefore, the user can install apps they never actually paid for, and the creator of the software can install potentially malicious apps without the user's knowledge.
From July of 2015 to February of 2016, three AceDeceiver iOS apps were uploaded to the official iOS App Store, posing as wallpaper apps and providing attackers with a fake authorization code to use in the AceDeceiver attacks.
A Windows iPhone management app called "Aisi Helper" that claimed to provide services like system backup and cleaning was installed by users in China, and it went on to install malicious iOS apps on connected devices. The apps were designed to be third-party App Stores with free content to bait users into using them and submitting their Apple IDs and passwords. Apple ID information was then uploaded to the AceDeceiver server.
Though Apple removed the original AceDeceiver iOS apps from the App Store in February (the ones used by the hackers to obtain the authorization codes), the attack remains active because attackers still have the authorization codes necessary to install fake apps on iOS devices. AceDeceiver only affects users in China, but Palo Alto Networks believes the AceDeceiver trojan or similar malware could spread to additional regions in the future. AceDeceiver is especially insidious as it has not been patched (and could work on older versions of iOS even when patched), installs apps automatically from an infected computer, and does not require an enterprise certificate.

AceDeceiver in its current incarnation requires users to download the Aisi Helper Windows app to their computers before the malware can spread to iOS devices, so people who have downloaded this software should remove it immediately and change their Apple ID passwords. In the future, AceDeceiver can be avoided by not downloading suspicious software.
Palo Alto Networks has a full rundown of AceDeceiver, its history, and how it works on the Palo Alto Networks website. It's well worth reading for anyone who wants more information about the malware.





















