Israeli mobile software developer Cellebrite gained media attention earlier this year when rumors suggested the FBI recruited the company to unlock San Bernardino shooter Syed Farook's iPhone. While the FBI did not enlist Cellebrite's help, the company does have technology licensed by governments that can extract iPhone data. ZDNet has obtained documents that reveal the scope of this technology.
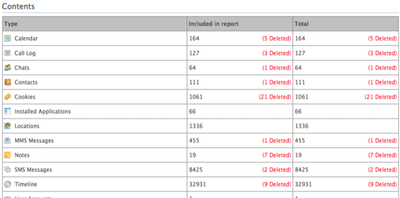
The leaked files are "extraction reports," which are organized to allow investigators to easily see and analyze data from a phone. Extraction is conducted by plugging the phone into a Cellebrite UFED device. While the device is primarily for extracting information currently on the phone it can, in some cases, extract recently deleted items. The phone at the heart of ZDNet's extraction report was an non-passcode protected iPhone 5 running iOS 8.
The first couple pages of the report include case numbers and unique identifying information for the device, including phone number, IMEI numbers and Apple ID. In these first pages, the report also divulges which plugins the software used to extract information from the device. These plugins can help the software extract data from QuickTime and iPhone backups.
The report compiles geolocation data from every photo taken on the device and visualizes it on a map, allowing an investigator to easily see when and where a person was. Text messages are organized in chronological order, which makes it easier for investigators to track conversations. The wireless networks a device has connected to are also logged, including the MAC address of the router, encryption type and the time last connected to the network.
Call log information includes whether the call is incoming or outgoing, the time, date, the other number on the call, and the duration of the call. Contacts, installed apps and user accounts on the device are also collected. Configurations and databases from apps, which include settings and cache data, are included in collection. Notes and voice mails are also extracted.
Finally, Cellebrite's technology includes an analytics engine that can figure out how many actions have taken place per phone number. For instance, it can tell investigators how many calls and text messages have occurred with each contact.
Cellebrite notes that its UFED device cannot crack passcodes on iPhone 4s and later. iPhone 5s and later come with a secure enclave co-processor that makes it even more difficult to crack for information. In November, Cellebrite signed a deal with the Indian government to provide technology to bypass locked iPhones.
Note: Due to the political nature of the discussion regarding this topic, the discussion thread is located in our Politics, Religion, Social Issues forum. All forum members and site visitors are welcome to read and follow the thread, but posting is limited to forum members with at least 100 posts.





















Top Rated Comments
So basically anyone not living under a rock can't be passcode cracked? Only their metadata stolen right?
Cellebrite: "ha ha ha ha ha"
What? Who cares then? Just have a phone newer than one that came out in 2012, or have a passcode and they can't get anything. Business as usual.