Mac owners who are still running macOS High Sierra 10.13 and who have already installed Apple's root security fix on that version of the operating system will need to install it once again upon upgrading to macOS 10.13.1, reports Wired.
Security researchers running a patched version of the original macOS High Sierra update, 10.13.0, told Wired that the root bug was reintroduced upon installing the macOS 10.13.1 update. After updating, they needed to install Apple's security patch again. Even that didn't fix the issue until their machines were rebooted.
Those who had not yet upgraded their operating system from the original version of High Sierra, 10.13.0, to the most recent version, 10.13.1, but had downloaded the patch, say the "root" bug reappears when they install the most recent macOS system update.
And worse, two of those Mac users say they've also tried re-installing Apple's security patch after that upgrade, only to find that the "root" problem still persists until they reboot their computer, with no warning that a reboot is necessary.
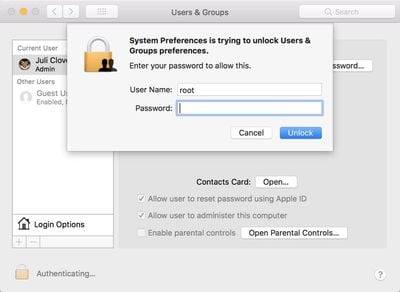
The root fix, released on Wednesday for macOS High Sierra 10.13.0 and 10.13.1, addresses a serious vulnerability that was first discovered a day earlier on Tuesday. The bug enabled the root superuser on a Mac with a blank password and no security check, letting anyone bypass the security of an admin account with the username "root" and no password.
While the security update successfully fixes the issue, it appears Apple may not have releases a modified and patched version of macOS 10.13.1, so customers who installed the update on 10.13 might think they're protected upon updating to 10.13.1, but they're not. Instead, the bug is fully re-introduced.
Apple may fix this problem now that the oversight has been pointed out, but in the meantime, customers upgrading from macOS High Sierra 10.13 to 10.13.1 should make sure to download the security update a second time and restart to be certain the root vulnerability is patched.
This won't be an issue when the macOS High Sierra 10.13.2 update is released, as Apple patched the bug in the macOS High Sierra 10.13.2 beta that was released this morning.