macOS users could be targeted with malicious attacks using Microsoft Office files that have macros embedded, according to details on the now-fixed exploit shared today by security researcher Patrick Wardle, who also spoke to Motherboard.
Hackers have long used Office files with macros embedded in them as a way to get access to Windows computers, but the exploit is also possible on macOS. According to Wardle, a Mac user could potentially be infected just by opening a Microsoft Office file that has a bad macro in it.
Wardle shared a blog post on the exploit that he found for manipulating Office files to impact Macs, which he's highlighting during today's online Black Hat security conference.
Apple fixed the exploit that Wardle used in macOS 10.15.3, so that particular vulnerability is no longer available for hackers to use, but it offers an interesting look at an emerging method of attack that we could see more of in the future.
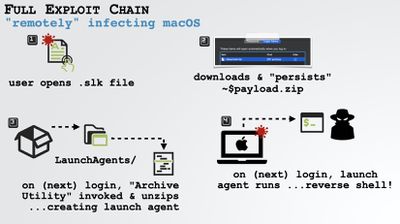
Wardle's hack was complicated and involved multiple steps, so those interested in full details should read his blog, but basically he used an Office file with an old .slk format to run macros on macOS without informing the user.
"Security researchers love these ancient file formats because they were created at a time when no one was thinking about security," Wardle told Motherboard.
After using the antiquated file format to get macOS to run a macro in Microsoft Office without letting the user know, he used another flaw that let a hacker escape the Microsoft Office Sandbox with a file that uses a $ sign. The file was a .zip file, which macOS didn't check against the notarization protections that prevent users from opening files not from known developers.
The exploit required the targeted person to log in to their Mac on two separate occasions as logins trigger different steps in the exploit chain, which makes it less likely to happen, but as Wardle says, only one person needs to fall for it.
Microsoft told Wardle that it has found that "any application, even when sandboxed, is vulnerable to misuse of these APIs," and that it is in contact with Apple to identify and fix issues as they arise. The vulnerabilities that Wardle used to demonstrate how macros can be abused have long since been patched by Apple, but there's always a chance that a similar exploit could pop up later.
Mac users are not invulnerable to viruses and should exercise caution when downloading and opening files from unknown sources, and sometimes, even known sources. It's best to stay away from suspicious Office files and other files that have shady origins, even with the protections that Apple has built into macOS.