A new report by security researchers Talal Haj Bakry and Tommy Mysk has revealed that link previews in messaging apps can lead to security and privacy issues on iOS and Android. Through link previews, Bakry and Mysk discovered that apps could leak IP addresses, expose links sent in end-to-end encrypted chats, download large files without users' consent, and copy private data.
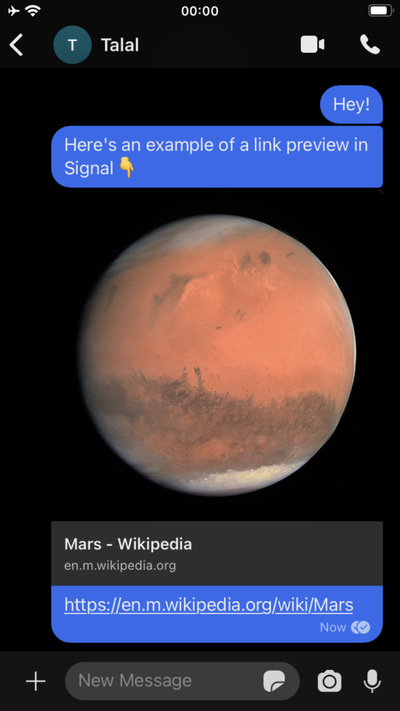
Link previews offer a peek at content such as web pages or documents in many messaging apps. The feature allows users to see a short summary and preview image inline with the rest of the conversation without having to tap on the link.
Apps such as iMessage and WhatsApp ensure that the sender generates the preview, meaning that the receiver is protected from risk if the link is malicious. This is because the summary and preview image are created on the sender's device and sent as an attachment. The receiver's device will show the preview as it was transmitted from the sender without having to open the link. Apps that do not generate a link preview at all, such as TikTok and WeChat, are also unaffected.
The issue arises when the receiver generates the link preview, because the app will automatically open the link in the background to create the preview. This occurs before users even tap on the link, potentially exposing them to malicious content. Apps such as Reddit generate links in this way.
For example, a malicious actor could send a link to their own server. When the receiver's app automatically opens the link in the background, it would send the device's IP address to the server, revealing their location.
This approach can also cause issues if the link points to a large file, whereupon the app may attempt to download the whole file, draining battery life and hemorrhaging data plan limits.
Link previews can also be generated on an external server, and this is how many popular apps such as Discord, Facebook Messenger, Google Hangouts, Instagram, LinkedIn, Slack, Twitter, and Zoom work. In this case, the app will first send the link to an external server and ask it to generate a preview, and then the server will send the preview back to both the sender and receiver.
However, this may pose a security threat when the contents of the sent link are private. Using an external server allows these apps to potentially create unauthorized copies of private information and retain it for a period of time.
Although many of the apps had implemented a data limit on how much of any link content to download, the researchers discovered that Facebook Messenger and Instagram were particularly notable for downloading the entirety of any link's contents to its servers, regardless of size. When questioned about this behavior, Facebook reportedly said that it considers this to be "working as intended."
Copies kept on external servers could be subject to data breaches, which may be particularly concerning for users of business apps such as Zoom and Slack, and those who send links to sensitive private data.
The research offers an appreciation of how the same exact feature can work in different ways, and how these differences can have a significant impact on security and privacy. See the full report for more information.